In today’s digital landscape, cybersecurity has become a crucial aspect of protecting businesses from the ever-evolving threat landscape.
Implementing effective cybersecurity practices can significantly reduce your business’s risk exposure and safeguard valuable assets.
The following article highlights the top 10 cybersecurity best practices that every business should adopt to strengthen their security posture and minimize the likelihood of cyber incidents.
Cybersecurity best practices:
Strong Password Policies
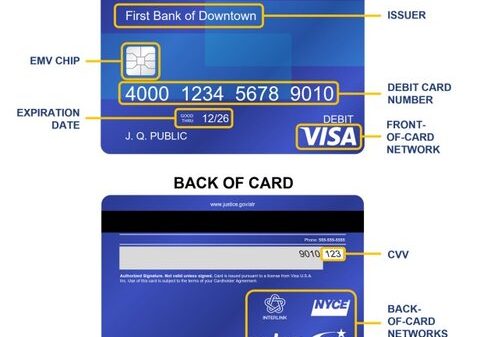
Creating complex and unique passwords is the foundation of strong cybersecurity. Encourage employees to use passwords that include a combination of letters, numbers, and special characters. Enforce regular password updates to mitigate the risk of compromised credentials. Implementing multi-factor authentication (MFA) adds an extra layer of security, requiring users to provide additional verification factors.
Employee Education
Employees are often the weakest link in the cybersecurity chain. Conduct regular cybersecurity training programs to educate your staff about common threats, such as phishing attacks. Raise awareness about the importance of identifying suspicious emails, attachments, and links. Encourage a culture of cybersecurity vigilance, where employees actively report potential security incidents and adhere to established security protocols.
Regular Software Updates
Timely software updates are critical for maintaining a secure digital environment. Software vendors release updates to address vulnerabilities and patch security flaws. Establish an efficient patch management process to ensure that all software and applications are up to date. Automating software updates where possible reduces the risk of human error and ensures the swift deployment of critical cybersecurity patches.
Secure Network Infrastructure
Securing your network infrastructure is essential for protecting sensitive data and preventing unauthorised access. Set up firewalls and intrusion detection systems to monitor and control network traffic. Secure Wi-Fi networks with strong encryption and change default passwords to enhance network security. Employ cybersecurity that regularly monitors network traffic and identify any anomalies or suspicious behaviour that may indicate a potential breach.
Data Backup and Recovery
Regular data backups are crucial for mitigating the impact of data loss in the event of a cybersecurity incident. Establish a comprehensive backup strategy by creating regular backup schedules. Store backups securely, preferably in encrypted form and off-site or in the cloud. Periodically test the restoration process to ensure the integrity of backed-up data and verify that critical systems can be recovered effectively.
Privileged Account Management
Implementing proper access controls is essential for limiting unauthorized access to critical systems and data. Utilize role-based access controls (RBAC) to assign permissions based on job roles and responsibilities. Restrict administrative privileges to only those who require them. Regularly review and revoke access rights for employees who no longer need them.
Secure Email Practices
Email is a common entry point for cyber threats. Implement email filtering and anti-spam measures to reduce the risk of malicious emails reaching employees’ inboxes. Educate employees about the importance of being cautious with email attachments and links, in addition verify the legitimacy of email senders before sharing sensitive information.
Secure Web Browsing
Secure web browsing practices are essential for mitigating the risk of malware infections and unauthorized data access. Encourage employees to use secure browsers with updated security features. Implement web filtering and content blocking to restrict access to potentially harmful websites. Educate employees about safe web browsing practices and the potential risks of visiting untrusted sites.
Regular Security Assessments
Conducting regular security assessments and audits helps identify vulnerabilities and weaknesses in your systems. Perform vulnerability assessments to proactively discover potential security flaws. Conduct penetration testing to simulate real-world attacks and evaluate the effectiveness of your security measures. It’s recommended you engage third-party experts to conduct comprehensive security audits to gain an unbiased perspective.
Incident Response Planning
Developing an incident response plan is crucial for effectively managing and containing cyber incidents. Establish clear protocols for detecting, reporting, and responding to security incidents. Test and refine the incident response plan regularly to ensure its effectiveness. Additionally, create a disaster recovery plan to facilitate the recovery of critical systems and data in the event of a cybersecurity incident.
Cybersecurity is an ongoing commitment that requires continuous monitoring, adaptation, and improvement to stay ahead of evolving threats. However, implementing these top 10 cybersecurity best practices significantly enhances your business’s ability to mitigate cyber risks.
It should also be taken into consideration that no matter the level of cybersecurity controls implemented you will never be 100% risk free. Threats posed from cyber criminals continue to evolve, therefore the measures employed may always be one step behind.
Good risk management dictates that a cybersecurity insurance policy should be arranged in conjunction with the above controls. An insurance policy can provide the financial resources required and access to incident response services who can mitigate the damage and help you recover from a cyberattack.
Read more:
Top 10 Cybersecurity Best Practices to Reduce Your Business’s Risk